"Building AI agents" is the easy part. The real question is "how do you actually run them?" Cohorte AI — a team behind 60+ enterprise agent deployments — packaged the six governance problems they hit every single time into six open-source libraries.
What is this stack, exactly?
Cohorte AI has shipped agents into 60+ enterprise environments. Across those deployments, they hit the same wall every time — not a model quality problem, but the system around the model being too vague to survive production.
The "Show HN" announcement points to six repos under the Cohorte-ai GitHub org. All Python, all Apache 2.0. They don''t replace orchestration frameworks like LangGraph or CrewAI — they sit on top, as a governance layer.
- Guardrails — Policy layer
Declare input, output, tool-call, and approval policies in YAML. Manage rules like "block prompt injection" or "auto-redact PII" as policy files instead of code. - Agent Auth — Identity & authorization
Not "can this user do X?" but "can this agent, acting on behalf of this user, do X to this resource right now?" — a delegated authorization model purpose-built for agents. - Context Router — Retrieval routing
Relevance scores alone aren''t enough. Combine permissions, token budget, and explainability to decide which context to pull in. - Context Kubernetes — Knowledge orchestration
Treat enterprise knowledge not as "doc search results" but as governed infrastructure. Permissions, freshness, and approval policies expressed declaratively in YAML. - Agent Monitor — Observability + killswitch
Beyond latency and throughput: detect cost blow-ups, refusal-rate spikes, approval bottlenecks, and auto-kill agents that breach thresholds. - TrustGate — Reliability certification
Turn "feels reliable" into "X% reliable with statistical guarantees" as a deployment gate. Self-consistency sampling + conformal calibration.
The core insight is simple. Agents don''t fail because the model is weak — they fail because the system around the model is ambiguous. That''s the pattern Cohorte saw across 60 deployments. Demo workflows that wow customers but collapse in production almost always lack answers to the same five questions: policy, identity, context, observability, reliability.
Why this matters now
OWASP published its first "Agentic AI Top 10" in December 2025 — goal hijacking, tool misuse, identity theft, memory poisoning, cascading failure, log agents. These are all operations problems. EU AI Act high-risk obligations kick in August 2026; Colorado AI Act enforcement starts June 2026. The infrastructure isn''t catching up to the regulation.
How is this different from orchestration frameworks?
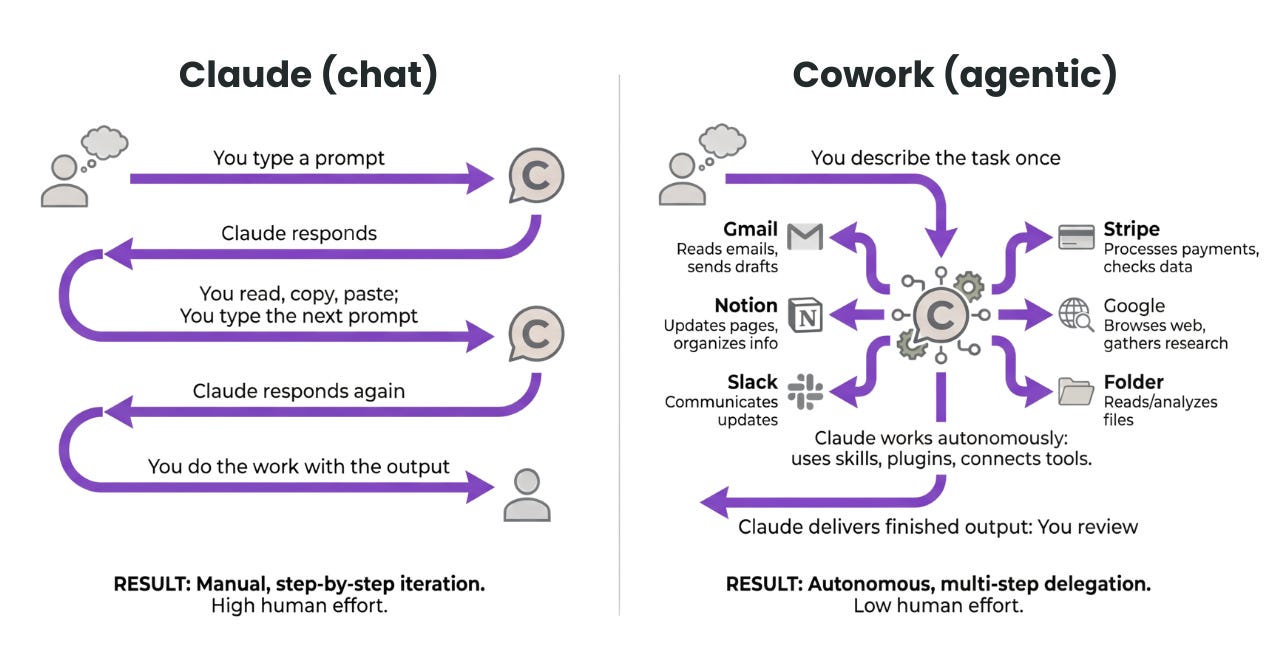
This is the most common confusion. LangGraph, CrewAI, OpenAI''s Agents SDK already exist — do we really need another framework? Answer: this isn''t a framework, it''s a governance layer.
| Orchestration frameworks (e.g., LangGraph) | Governance stack (Cohorte 6-library) | |
|---|---|---|
| Role | Build the workflow | Make the workflow controllable |
| Core question | "What does the agent do?" | "What is the agent allowed to do?" |
| Policy | Scattered across code | Declarative YAML in one place |
| Identity | Mostly reuses human IAM | Purpose-built delegated agent identity |
| Observability | Traces + metrics (post-mortem) | Killswitch + cost thresholds (runtime control) |
| Reliability | Test pass/fail | Reliability score with statistical guarantees |
| Deployment gate | "Ship if it feels good" | "Ship if reliability > 90%" (CI/CD gate) |
The actual design intent is to combine an existing orchestrator with this governance layer. When a user says "summarize this contract and recommend it to procurement," Guardrails checks policy, Agent Auth verifies delegated permissions, Context Router picks relevant sources, Context Kubernetes governs knowledge, the workflow runs on LangGraph, Agent Monitor watches cost and anomalies, and TrustGate backstops the deployment with a certified reliability score for that workflow class.
That''s the difference between a demo and a production system. One earns applause in a sales meeting; the other passes a review meeting.
The interesting part is the simultaneity. Microsoft also open-sourced its Agent Governance Toolkit in April 2026 under MIT. Seven packages applying OS-kernel, service-mesh, and SRE patterns to agents — its policy engine intercepts every agent action with sub-0.1ms latency. It''s the first toolkit to map every category of OWASP''s Agentic Top 10.
Traditional IAM vendors like SailPoint and Okta are rolling out "agent identity governance" frameworks too. This isn''t coincidence. Agent Ops is hardening into a distinct infrastructure layer.
How to actually start
- Pick the single most painful governance area
Don''t install all six. If you have permission incidents, start with Agent Auth. If costs leak, start with Agent Monitor. If outputs are inconsistent, start with TrustGate. Cohorte explicitly recommends "incremental adoption." - Write one policy line in YAML
For example, in Guardrails, just add ablock-prompt-injectionrule that filters "ignore previous instructions"-style patterns.pip install theaios-guardrailsand you''re running in 30 minutes. - Agree on killswitch thresholds with non-engineers
Agent Monitor''s essence is rules likecost_per_minute > 5.0 → kill. Don''t let an engineer set this alone — agree on it with PMs and finance. That negotiation is the actual governance. - Make reliability a deployment gate
TrustGate plugs into CI/CD withtrustgate certify --min-reliability 90 --yes. Below 90%? Build fails. That''s how you turn "vibes" into a number. - Cross-check with Microsoft''s toolkit
Microsoft''s Agent Governance Toolkit solves the same problem with explicit OWASP Top 10 mapping and adapters for LangChain, CrewAI, LangGraph. Both are MIT/Apache 2.0 — pick the one that fits your stack.
Where this stack falls short
Atlan''s framework points out that effective agent guardrails need five layers — data/context, design-time governance, runtime guards, identity/access, and human oversight. The Cohorte stack covers runtime + part of design-time. Without "AI-ready data" underneath, no governance layer will save you. Gartner predicts 60% of AI projects will be abandoned for lack of AI-ready data. A governance stack sits on top — it doesn''t fix the data problem for you.
Want to go deeper?
Show HN announcement The original 6-library release post, derived from 60+ deployments — community reactions in the thread news.ycombinator.com
Cohorte AI GitHub org trustgate / guardrails / context-router / context-kubernetes / agent-monitor / agent-auth — all in one place github.com
The Enterprise Agentic Platform playbook Charafeddine Mouzouni''s free architecture blueprint covering the stack''s design intent and integration patterns cohorte.co
Microsoft Agent Governance Toolkit A 7-package open-source toolkit applying OS-kernel, service-mesh, and SRE patterns to agents — full OWASP Top 10 mapping opensource.microsoft.com
Atlan — AI Agent Risks & Guardrails guide The 5-layer guardrail model, the AWARE framework, and how it ties into data governance atlan.com
SailPoint — Governing AI Agents framework An IAM vendor''s view on stopping agent identity sprawl and permission drift sailpoint.com