AI found over 500 high-severity security vulnerabilities that had been hiding in open-source code for decades. Bugs that experts had reviewed for years and still missed. The next day, cybersecurity stocks dropped in unison.
What Is It?
On February 20, 2026, Anthropic announced Claude Code Security. It's a security vulnerability scanning feature built into Claude Code (Anthropic's AI coding tool), and its approach is fundamentally different from traditional security tools.
Traditional static analysis tools store known vulnerability patterns in a database and match code against them one by one. They're good at catching common issues like exposed passwords or outdated encryption, but they often miss complex vulnerabilities like business logic errors or authentication bypasses.
The core idea behind Claude Code Security is that it "reasons through code the way a human security researcher reads it." It understands how components interact, traces how data flows through the application, and catches context-dependent vulnerabilities that rule-based tools miss.
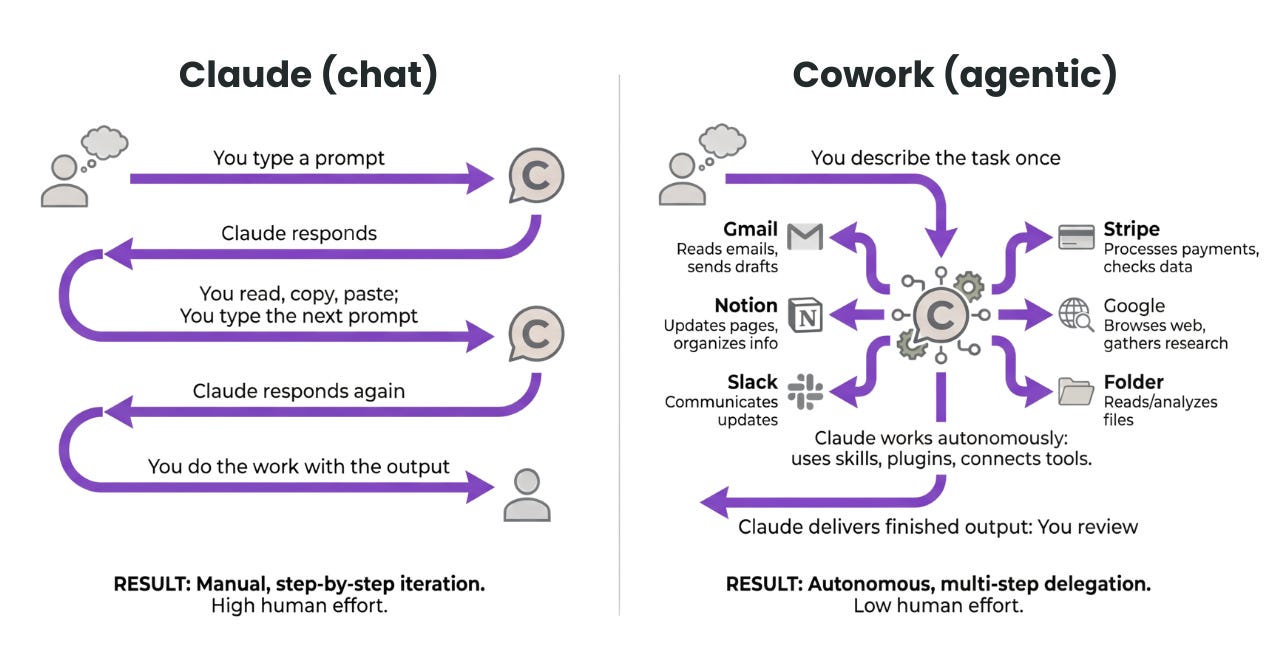
In an exclusive interview with Fortune, Anthropic Frontier Red Team leader Logan Graham said: "Thanks to Opus 4.6's agentic capabilities, the AI explores codebases step by step, tests each component's behavior, and follows leads — much like a junior security researcher would, except far faster." He described the tool as a "force multiplier" for security teams.
In practice, when Anthropic used Opus 4.6 internally to scan production open-source projects, it uncovered over 500 high-severity vulnerabilities that had gone undetected for decades despite expert review. These included memory corruption, injection vulnerabilities, authentication bypasses, and complex logic errors — all currently going through responsible disclosure with the open-source maintainers.
Key Point
Claude Code Security never auto-applies patches. Every finding goes through multi-stage verification before appearing on the dashboard with a severity rating and confidence score. Fixes are only applied after a developer reviews and approves them.
Currently available as a research preview for Enterprise and Team customers, with free priority access for open-source repository maintainers.
What's Different?
The security tools market is being disrupted. Let's compare traditional static analysis tools with Claude Code Security.
| Traditional Static Analysis | Claude Code Security | |
|---|---|---|
| Detection Method | Known pattern rule matching | AI reads and reasons through code |
| Detection Scope | Common vulnerabilities (SQL injection, XSS, etc.) | Extends to business logic errors, auth bypasses, and more |
| False Positives | High → causes analyst fatigue | Filtered via multi-stage self-verification |
| Result Explanation | Rule ID + location info | Natural language explanation + patch suggestion |
| Remediation | Manual patch writing | AI-suggested patch → human approval |
The market reaction was immediate. On announcement day, February 20th, cybersecurity stocks dropped across the board.
| Ticker | Drop | Sector |
|---|---|---|
| SailPoint | -9.4% | Identity Security |
| Okta | -9.2% | Authentication/Identity |
| Cloudflare | -8.1% | Web Security/CDN |
| CrowdStrike | -8.0% | Endpoint Security |
| Zscaler | -5.5% | Cloud Security |
| Palo Alto Networks | -1.5% | Network Security |
| BUG ETF | -4.9% | Global Cybersecurity ETF, lowest since Nov 2023 |
According to Benzinga, the market's core concern is this: AI is evolving from an "assistive tool" to a "direct replacement for specialized security software." Doubts are growing about legacy security vendors' long-term pricing power.
This is the second enterprise software sell-off Anthropic has triggered this year. The first came with the Claude Cowork plugin launch in late January. Competitor OpenAI also released a similar automated security tool called 'Aardvark' in October 2025. Aardvark tests vulnerabilities in an isolated sandbox and even estimates how difficult they'd be for hackers to exploit.
The bottom line: the market's verdict is "if AI can do what security engineers do, then companies selling security software have a problem." Both AI companies have signaled CI/CD pipeline integration, which could penetrate the core territory of existing security vendors.
Quick Start Guide
It's currently in research preview so there may be a waitlist, but here's what the flow looks like.
- Check Your Plan
You'll need a Claude Enterprise or Team plan. Open-source project maintainers can apply for free priority access. - Request Access
Apply for the research preview at claude.com/contact-sales/security. You'll collaborate directly with Anthropic's team to refine the tool. - Connect Your GitHub Repository
Link the GitHub repository you want scanned to Claude Code Security and request an AI security review. - Review Results on the Dashboard
Discovered vulnerabilities are displayed with severity ratings, natural language explanations, and confidence scores. Address them in order of priority. - Review & Approve Patches
Click "Suggest Fix" to see the AI-proposed patch, then approve if it checks out. All fixes require human final approval.
Heads Up
This is still in research preview. CI/CD pipeline integration isn't supported yet, and availability is limited. Approach this for evaluation and feedback purposes rather than full-scale adoption.