One username. That's all it takes to automatically scan 3,000 sites for someone's digital footprint — pulling in profile photos, names, bios, locations, emails, and phone numbers into a PDF dossier. And as of yesterday (May 5th), flip on the new --ai flag and an OpenAI-compatible model will summarize who this person appears to be.
The tool is called Maigret, named after the French detective in Simenon's novels. 25.5k GitHub stars, MIT license, free with no API key needed. It started as a spiritual successor to Sherlock, but the scope and depth are in a completely different league.
What Is It?
Maigret is an OSINT (Open-Source Intelligence) tool that automatically builds a dossier on a person from just a username. One blogger put it well on May 2nd, 2026: "A nickname is all you need. No email, no phone number, no real name required".
Setup is one line.
- Install + run immediately
pip install maigret→maigret your_username. By default it scans the top 500 sites by traffic — add the-aflag to hit all 3,000+. - Choose your report format
HTML (--html), PDF (--pdf), XMind mind map (--xmind), JSON/CSV, or an interactive D3.js graph (--graph). Pick whatever fits your workflow — investigation, CTF, internal security audit. - Profile data extraction, not just presence detection
It doesn't just tell you "account exists." It scrapes profile pages for name, photo, bio, location, follower count, join date, and links to other accounts — via socid_extractor. - Recursive search
When it finds another username, email, or link on a profile page, it automatically feeds that as a new input and searches again. Alt accounts, real-name accounts, and email variants all get chained together automatically.
Don't want to install anything? Use the Telegram bot (@maigret_search_bot) — no Python environment needed. It also runs on Cloud Shell, Colab, and Replit.
How Is It Different from Sherlock?
Sherlock (60k+ GitHub stars) is probably the best-known OSINT username tool out there. But here's the thing — Maigret is fundamentally different.
| Feature | Sherlock | Maigret |
|---|---|---|
| Coverage | ~400 sites | 3,000+ sites, auto-updated on GitHub every 24h |
| Output | Presence only (account exists / doesn't) | Name, photo, bio, location, email, linked accounts |
| Recursive Search | None | Auto-searches discovered usernames and IDs |
| Network Routing | Direct HTTP/HTTPS | Tor, I2P, SOCKS proxies — searches .onion and .i2p sites too |
| Report Formats | Text, CSV | HTML, PDF, XMind, JSON, D3.js graph |
| Blocking & CAPTCHAs | Gets blocked, stops there | Partial bypass, per-site detect/bypass logic built in |
| AI Integration | None | --ai flag routes results to any OpenAI-compatible API for summary (added 2026-05-05) |
Bellingcat lists Maigret as a separate entry in its own OSINT toolkit. The picture is becoming clear: Sherlock keeps its spot as the quick, free option — Maigret is becoming the standard for professional OSINT workflows.
The New AI Mode: What Does It Actually Change?
PR #2620 on May 5, 2026 officially documented the --ai flag. The mechanics are straightforward.
- Step 1: Raw results get converted to a markdown report
After scanning 3,000+ sites and completing recursive searches, the raw data is converted into model-friendly markdown. - Step 2: That markdown gets sent to an OpenAI-compatible chat completion endpoint
Defaults to OpenAI. Setopenai_api_base_urlto point it at Azure OpenAI, OpenRouter, or a local LLM server. - Step 3: The model generates a short investigation summary
Likely real name, location, occupation, interests, languages, confidence level, and follow-up leads. It outputs both the estimates and recommended next steps. - Step 4: Streams straight to your terminal
Per-site scan logs are suppressed — only the model's output flows to stdout. One line:maigret user --ai --ai-model gpt-4o-mini.
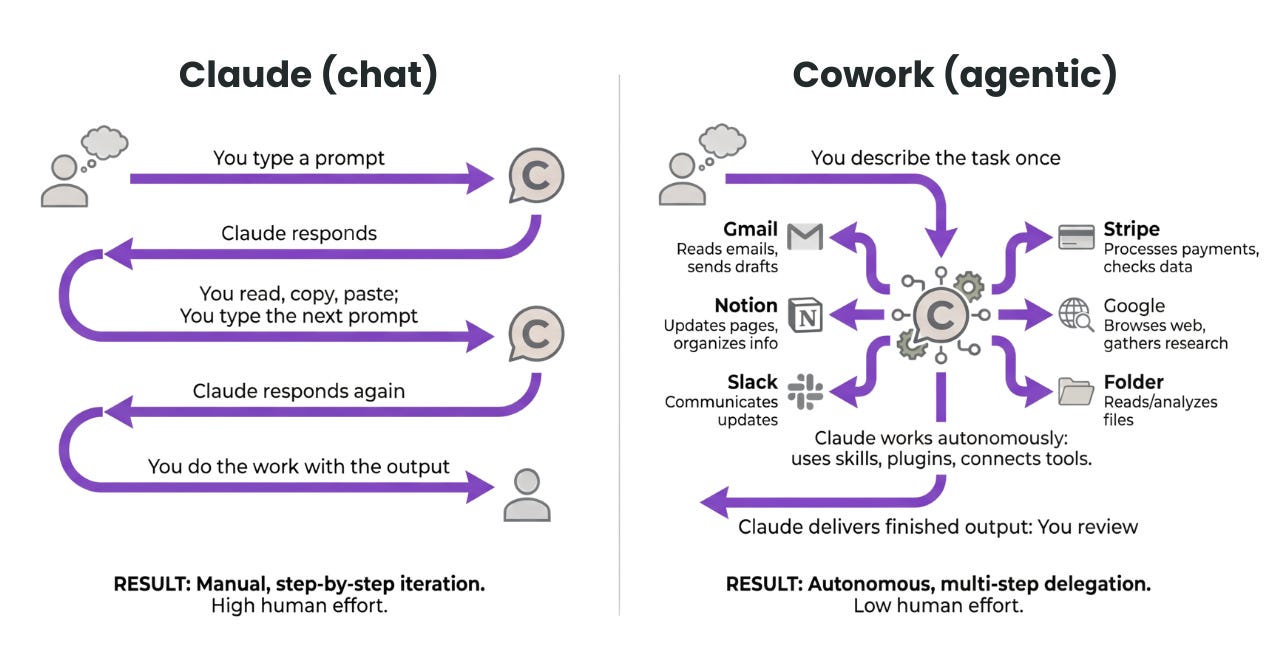
Here's the thing — this one-line change matters. Maigret shifts from a simple data collection tool to an automated investigation synthesizer. The 30-minute manual step of assembling a dossier from raw data disappears entirely. And the risk profile goes up proportionally: the balance of who can build a dossier on whom, cheaply and quickly, just shifted.
What Changes for Korean Organizations?
"We don't do OSINT" isn't the point. Your employees' and customers' information is already an OSINT target. The ease of these tools has crossed a threshold — exposure audits need to become part of default operations.
That said, the legal context in Korea matters here. Under Korea's Personal Information Protection Act and the Network Act, automatically aggregating and combining someone else's information without consent can be a legal problem — even if each piece is publicly available. Purpose needs to be explicit: self-auditing, formally authorized security assessments, CTF or research use.
- Step 1: Self-OSINT — give employees a guide to audit themselves
Have employees run Maigret on their own email or username to check their digital footprint. Don't mandate it — distribute it as a security training resource. "Find old accounts you should delete" is the lowest-friction entry point. - Step 2: Quarterly exposure checks for executives and VIPs
With explicit consent and through the security team, run quarterly checks on the CEO, CFO, and key engineers. Reduce the surface area for blackmail, phishing, and social engineering first. Document the OSINT scope, retention period, and data handling in the engagement contract. - Step 3: Integrate into internal red team exercises
When building phishing simulations, use Maigret to build a real dossier on one consenting employee in under an hour. Showing "this is what someone can build on you in 5 minutes" is 10x more effective than any OSINT awareness slideshow. - Step 4: Pre-hire vetting for executives and key talent (Tor and dark web included)
With prior written consent, outsource external reputation checks for senior hires. Since Maigret covers Tor and I2P, dark web exposure is included in the same tool — potentially replacing a separate dark web monitoring service.
Getting Started
- Step 1: Run it on yourself first
Takes about 15 minutes.pip install maigret && maigret your_username --html. Open the HTML report and check the list of accounts you'd forgotten existed. - Step 2: Classify by risk
(a) Active accounts — check for password reuse. (b) Dormant but live accounts — delete them now. (c) Accounts that expose your employer, real name, or location — clean up the profiles. - Step 3: Get your own AI-generated dossier
export OPENAI_API_KEY=... && maigret your_username --ai. The model summarizes who you appear to be based on your public footprint. It's the fastest way to get an objective read on your external persona. - Step 4: Design a formal security audit process
Add quarterly OSINT checks for executives and key staff to your security vendor engagement. Build an SOP: subject consent → define scope and retention period → regular reporting → data destruction. - Step 5: Write a one-page internal OSINT policy
Cover what's permitted and what's off-limits. Self-audits: fine. Checking employees without consent: prohibited. Executive OSINT: requires sign-off from both the security team and legal.
Deep Dive Resources
Maigret Official GitHub README 25.5k stars, MIT license. Complete docs covering installation, CLI options, web UI, Docker, Tor/I2P routing, and the AI analysis mode — including the newly documented --ai and --ai-model flags github.com/soxoj/maigret
Korean Practitioner's OSINT Writeup (2026-05-02) A hands-on walkthrough of Maigret in practice. Covers which use cases are legally safe in Korea and where Korean site coverage falls short jkf87.github.io
Bellingcat OSINT Toolkit — Maigret Entry See how the investigative journalism community's standard OSINT toolkit classifies Maigret. Useful for understanding where the tool sits in a professional investigation workflow bellingcat.gitbook.io